Digital voting systems are shockingly vulnerable to attacks and manipulations. For the credibility of the democracy, this is not good news. The solution is both digital and analog.

After the tight election results, only the Defeated are not always shake more often surprising the mind: How such a result comes about? Why were the predictions so wide of the mark? Went to really do anything with the right things? Alone, these doubts are poison for any democracy, shaking you to the main pillars of our political system: The basic trust in the legitimacy of the decision and respect the decision of the majority.
For years, the concern of voters, or equal to, all the elections could be manipulated either by political opponents or by outside powers is growing. And even if it is not possible to influence the outcome of the elections, attempts to tamper, at least, irritation or uncertainty. They sow the seeds of doubt in the decision and thus also of democracy itself. And the in times in which democracy powerful adversaries facing – be it autocrats, populists, or other opponents of pluralism.
Pioneering congressional elections in the United States
Discussions and a queasy feeling it is, therefore, certainly also in the US Congress elections on may 6. November, when all 435 members of the U.S. house of representatives and a third of the members of the Senate are elected. Especially in such a divided Nation, the Defeated will feel a sense of uncertainty. Observers do not make but only the manipulation-prone electoral system, but also the President personally.
In the last presidential election winner Donald Trump had not recognized the official election result, initially, because he had to get the necessary majority in the electoral, but not the most votes. The did not want to accept the Trump. The Commission appointed brought no clarity. Trust in the elections, however, was shaken in a sustainable way. An elected US President that was formerly referred to once as the leader of the free world, to doubt one’s own election system, in spite of its profits – an indictment of democracy.

US President, Donald Trump questioned despite the victory, the reliability of the US elections
For years, the United States fear a Manipulation of the elections by foreign powers. Since the last presidential election, the notes are condensed. Russia has a massive shuffle. Russian trolls have been systematically spreading a dozen false reports in the social networks, hackers launched a cyber attack on the data of the National Committee of US-Democrats and the unflattering published emails of opponent Hillary Clinton.
In addition, there is solid evidence of manipulation attempts, such as the scandal of the Cambridge Analytica was impressive. The company had manipulated about Facebook targeted voters in the United States and, indirectly, the Brexit vote influenced. It was “almost certain, that systematic fraud and voter deception happened,” said Whistleblower Christopher Wylie at a hearing in the European Parliament. “Facebook’s System allowed for this.”
Easily manipulated voting machines
An attempted influence, however, is something else than an actual Manipulation of election results. The vulnerability of the current voting machines in the United States are demonstrated by J. Alex Halderman, a Professor of Computer science at the University of Michigan. He tirelessly explains to his students, and the media, as easy to the at the upcoming Congress election used voting computers can be manipulated. On a choice computer, Halderman has the game Pac-Man, in order to demonstrate how little the System is protected.
At a hearing in the US Congress Halder, a man urgently warned of the vulnerability of the system. “The government and Congress need to immediately improve election security, before it is too late,” urged Halderman on Twitter. Despite the admonishing words of the insecure voting machines, Accuvote-TS and TSX are also used in the Congress election again in almost 20 States.
Wrong Lessons from the election debacle?
With the introduction of the voting machines, the Americans wanted to respond to, among other things, to the awkward choice of drama in the year 2000. At that time, only a tiny majority decided on the presidency of the Republican George W. Bush, Democrat Al Gore drew the short straw.
The heated election was run, but the result had yet to be made, because many of the back then used punch cards were not stamped clearly. 36 days and nights, the USA and the whole world looked to the election officials in Florida, the examined with a magnifying glass the unclear punched hole cards.
Then the close election victory of Bush, however, did not bring the results anyway. Finally, Bush’s lead was around six million votes cast in Florida, only 0.008 per cent. Due to the unreliable punch card System, more than 100,000 votes were declared invalid because they were not assigned to without a doubt.

Pac-Man for President? In the USA voting machines are particularly easy to hack.
As a lesson from the debacle of Florida in 2004 introduced a selection procedure by the Computer. In the congressional elections, about one-third of all registered voters will cast their vote digitally. The Rest makes the cross analog or punches more holes.
Hacking is a kids game
How easy the choice procedure are hack by Computer, showed up at the DEFCON 26, one of the leading Hacker fairs, held in August in Las Vegas. The organizer praised the contest for the Hacker-young: Who cracks the fastest, the safety technology of the websites of the electoral authorities, has won. On the websites of election authorities, voters to be registered, and over the nearest electoral office informs. In addition, the results will be submitted on the day of the election.
For the competition, exact copies of the electoral authorities pages Florida, Iowa, Michigan, New Hampshire, Ohio, Pennsylvania, Virginia and Wisconsin were created. The eleven-year-old Audrey Jones, it took just ten minutes until he had one of the sites is hacked and the page structure was penetrated. There, he would have been able to arbitrarily change the names of the candidates or the number of votes. On the whole, according to the organizers, more than 30 children to hack the copied web pages in less than half an hour.
Europe is also threatened
The Problem there is not only in the United States: the European systems are not immune to attacks or manipulation. The have shown not only the machinations of the company Cambridge Analytica. Also in France, were widely used in the last presidential election shortly before the election, thousands of internal documents of the candidate, Emmanuel Macron. The perpetrator had hacked by Macrons election campaign team-internal information, such as your E-Mails, invoices and contracts, and the net.

Facebook CEO Mark Zuckerberg made before the US Congress (photo), and the EU Parliament only vague Commitments
EU Commission President Jean-Claude Juncker warned in mid-September in his speech to the situation of the European Union to take account of possible manipulation of the Europe in next year’s elections. “We must protect free and fair elections in Europe. Therefore, the Commission is today proposing new rules to our democratic processes against Manipulation by third States or private interests.”
Serious gaps in security in the last Federal election
Germany is afraid also from possible tampering, and cyber attacks. How justified is this concern that show thousands of hacker attacks daily, on companies, infrastructure and public facilities. Successful cyber attacks on the Bundestag and the data network of the Federal government. The attackers had pushed into the deep into the System, so that the entire Bundestag-IT had to be replaced.
Behind it to plug in according to the findings of the UK’s cyber defence of the Russian military intelligence service GRU, and more precisely with the GRU-related hacker group “APT28”, the UK’s National Cyber Security Centre said. London published a list with a total of twelve Russian hacker groups, those of the GRU. According to the estimates of British, Dutch and US security authorities, these groups are also available for the cyber-attacks on the world Anti-Doping Agency (WADA), the Organisation for the prohibition of chemical weapons (OPCW) and many other attacks responsible.
The Cold war is raging in Cyber-Space
Despite the dangers, many areas are protected insufficiently, the authorities regularly. How easily a choice can be manipulated, demonstrated in the last year of the Darmstadt computer science Student Martin Tschirsich. Without much effort he found the actually-protected Software program “PC-choice” on the Internet. He felt not only the appropriate instructions, but also the corresponding passwords in the network.
So the resourceful Student gained access to the sensitive Code of the Software – and could have had an easy game. But Tschirsich the authorities informed about the serious security gaps. The Federal returning officer and the Federal office for security in information technology (BSI) is turned on and the Software has been withdrawn from the market.
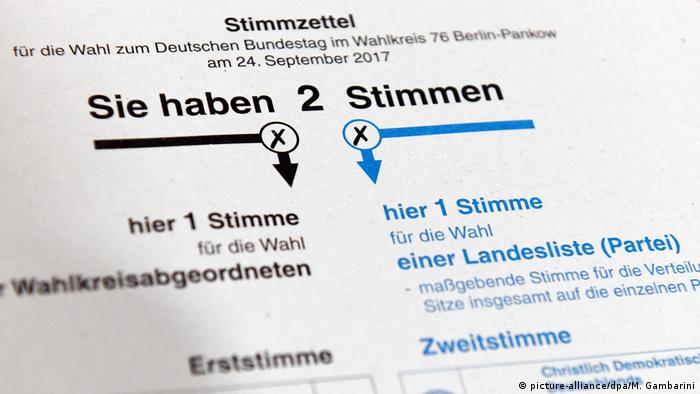
Analog and slow, but reliable: a ballot paper in paper form
As good as any Software can sooner or later be hacked. A one-hundred-percent secure System, it will probably never. However, a well-fortified democracy and a reliable electoral system needs. As for despots, and autocrats of free, fair and secret elections remain a horror. For this reason, in the digital age, according to the hack of Professor Halderman’s over no way, in addition to the electronic choice in addition to the classic and analog, on paper, to the vote.
Of course, there are still countless possibilities for manipulation. Additional ballots can disappear, appear or regular ballot somewhere. The digital Transmission of the analog results to the Central election Commission is also open to manipulation. In the case of justified Doubt, it would be so, however, the possibility of a recount.