The FIDO Alliance has released the first version of the FIDO specification is released. With the standard, developers can easily onlineauthenticatie without adding passwords to apps. Among others, Microsoft and Google support the alliance.
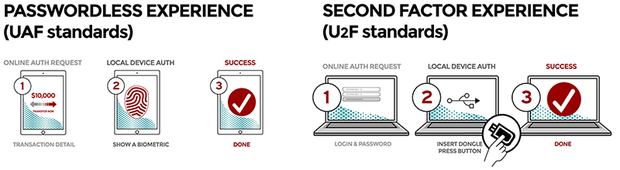
It involves two specifications, which are now out of the testing phase are removed: UAF and U2F. UAF is the basis and the specifications describe, among other things, the protocols, the procedures, the apis for the client and the Authenticator components. The U2F standard consists of everything you need for tweetrapsauthenticatie, which, in addition to an online login an additional authentication method such as a dongle is required. With this last the online login easier expired, such as via a four-digit pin.
Developers can now get down to the open standard to deploy in their apps and services. FIDO, which stands for Fast IDentity Online, was founded in 2012 to an open, interoperable, and scalable set of mechanisms that for a replacement of passwords for onlineauthenticatie to take care of.
FIDO operates on the basis of public key cryptography, such as PGP for encrypting mail. Developers can use an authentication method to choose no matter whether it is voice recognition, fingerprint, chip or face recognition. When using a key pair is created and the FIDO-standard controls then the encrypted storage of the private key and the public key on a server.
A large number of techgiganten has behind the standard itself, such as Google, Samsung, Yahoo, Microsoft, Qualcomm, VISA, and RSA. So, Google uses it for his experiments with usb-sticks in order to log in and Samsung for are mobile finger print scanner. The basis of FIDO was formed by the company Nok Nok Labs.
